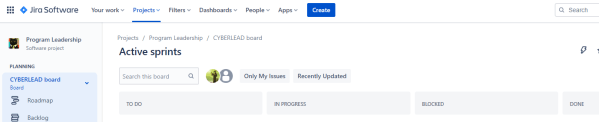
Over the past seven-ish years I’ve developed my own system for managing work from an executive perspective down to the individual contributor, and after some prompting from a friend (thanks MadHat!) I realized this might be helpful to others. Just to level set, the intent of this approach is to grow a full work management solution from nothing to the point where you can dynamically manage workloads and commitments, and to do so in a continuously evolving and improving way. As with anything agile… fail early, fail often, and go with what works for you and your teams. 🙂
Continue reading “Jira for Business Management”Pwnagotchi Waveshare V3
So you want to build yourself one of those Pwnagotchi that everyone is talking about since the Flipper Zero came out and no one can get one, eh? And you’ve followed the official installation instructions (which this post supplements, but does not replace) but have noticed that either (1) you can’t really find a Waveshare eInk 2.13″ display that’s not version 3, or (2) you can’t quite seem to get into your Pwnagotchi if it’s even running and ERMAGERD WTF why is this so obtuse? Well, this is the guide for you. 🙂
Continue reading “Pwnagotchi Waveshare V3”Intro to BurpSuite
I recently had cause to make some training on how to get and perform some basic operations using BurpSuite, so I thought I’d share here. As always, feel free to use as you’d like. 🙂
DerbyCon 9 – DomainTools CTF – Reversing
Part three of the DerbyCon DomainTools CTF write-ups. You can find coverage of all the Crypto challenges here and coverage of all the Forensics challenges here. This finishes up the solutions for every challenge in the CTF, broken up by the same section names that they used. When possible, I’ll also be creating CyberChef recipes to directly solve each challenge, and linking to them following the solution description. Let’s get started!
Analyzing Multiple APKs At Once
This falls into that series of things where I had to make something work when there wasn’t a pre-built package, so I’m documenting it here in case (1) I ever need to do this again, or (2) someone else can benefit from it. Let’s say you’re looking into a device that runs on Android, and it has a bunch of APKs that you have no clue what to do with… why not use some common tools to quickly process all of those files?
Quick-Hit: Editing Submissions in BurpSuite
Let’s say you’re running some tests on a service and want to use some characters that aren’t standard in your systems’ character set. How do you do that?
Continue reading “Quick-Hit: Editing Submissions in BurpSuite”
Gpg4win/Kleopatra for Windows
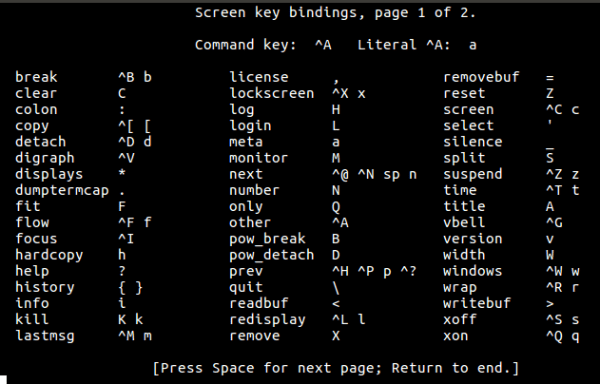
Quick Hits: Screen
Ever been frustrated by a session that was running remotely when your SSH/nc/1337shell.phpaspxcf dropped, and all that work was wiped out in the blink of an eye because when that died your shell did too, and the OS was nice enough to clean it all up?
Yeah, it sucks. Fortunately, there’s an easy way to handle that, and it’s called “screen”. Let’s dive in.
Continue reading “Quick Hits: Screen”
Proxmark3 RDV 4
So… I got a Proxmark3 RDV 4 for Christmas. It’s great. It’s tiny, svelte, and… had a bunch of errors right out of the box. Naturally that means it’s time to reflash it, but as it turns out the default wiki instructions for Kali Linux aren’t quite right for the RDV 4 now. Let’s fix that, shall we?
Quick Tip: Linux and Rufus
Just learned today:
If you are making a bootable disk from a Linux distro using Rufus and it won’t mount, try creating it using the DD option.
Apparently, Linux sometimes only likes its own tools being used on it.
Bonum Venandi,
KS