It’s been three months since the “Double Digits” challenge was released at Dallas Hacker’s Association (DHA), so it’s time to reveal the solution. If you haven’t played it yet and would like to, you can find the challenge here. Continue past the break if you’re ready to see the full solution!
Continue reading “DHA Challenge 2023-06 (Solution)”DHA Challenge 2023-05 (Solution)
It’s been three months since the “Mystics and Magicians” challenge was released at Dallas Hacker’s Association (DHA), so it’s time to reveal the solution. If you haven’t played it yet and would like to, you can find the challenge here. Continue past the break if you’re ready to see the full solution!
Continue reading “DHA Challenge 2023-05 (Solution)”DHA Challenge 2023-04 (Solution)
It’s been three months since the “Unselected Keys” challenge was released at Dallas Hacker’s Association (DHA), so it’s time to reveal the solution. If you haven’t played it yet and would like to, you can find the challenge here. Continue past the break if you’re ready to see the full solution!
Continue reading “DHA Challenge 2023-04 (Solution)”Jira for Business Management
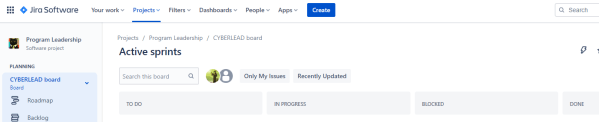
Over the past seven-ish years I’ve developed my own system for managing work from an executive perspective down to the individual contributor, and after some prompting from a friend (thanks MadHat!) I realized this might be helpful to others. Just to level set, the intent of this approach is to grow a full work management solution from nothing to the point where you can dynamically manage workloads and commitments, and to do so in a continuously evolving and improving way. As with anything agile… fail early, fail often, and go with what works for you and your teams. 🙂
Continue reading “Jira for Business Management”Pwnagotchi Waveshare V3
So you want to build yourself one of those Pwnagotchi that everyone is talking about since the Flipper Zero came out and no one can get one, eh? And you’ve followed the official installation instructions (which this post supplements, but does not replace) but have noticed that either (1) you can’t really find a Waveshare eInk 2.13″ display that’s not version 3, or (2) you can’t quite seem to get into your Pwnagotchi if it’s even running and ERMAGERD WTF why is this so obtuse? Well, this is the guide for you. 🙂
Continue reading “Pwnagotchi Waveshare V3”Custom Proxmox VE LXC Images
Using Linux Containers can significantly improve deployment times to make customized instances of a system. For instance, you may want to create 10 unique instances of a system for training purposes, but don’t want to run custom code on each when it starts to generate key material, assign users, etc. Using Linux Containers can make that simple, but unfortunately it’s not always so simple to create that custom image for deployment. This post is going to cover the start to finish customization of an image (in this case, using Kali Linux) from the base image to one that can deploy in a non-privileged virtualization platform (in this case, Proxmox VE). Let’s get started!
Continue reading “Custom Proxmox VE LXC Images”Hermit’s Hardware Hacking Box
Have you ever wanted to get into hardware hacking as well as offensive security, but didn’t know how to get started? Good news! For a recent meeting of the Pittsburgh Hacker’s Association I put together a presentation on how to setup the standard box I use for almost everything. It’s a dual-boot system with both Ubuntu and Kali, a shared data partition, and all the tools you could ever need pre-configured and installed. If you want to get started, just grab the PDF and get going!
Good hunting! 🙂
Starting the 2020 eChallenge Coin Redux
There’s a designer named Bradán Lane who makes some excellent hardware, and one of my favorite things he’s created is a set of challenge coin circuits. I won’t go into too much detail on them other than to note they have a fun story line, a series of challenges, and you have to exercise some basic hardware hacking skills to participate. If you’d like more details, please check out the listing for the coin on Tindie. But what if you don’t know how to get started? Well, a friend of mine (Visual) and I recently played through this, and thought we’d document how to get started for anyone who needs a little extra help. Let’s get started!
Continue reading “Starting the 2020 eChallenge Coin Redux”Closing out Lightning to Bitcoin
Maybe you’ve decided that you want to close down your old computer that was running a Lightning network node, but you haven’t decided to stop using Bitcoin. Maybe you just need to pay for an unexpected expense. Maybe anything. The question becomes: How do you take the BTC you currently have linked into a Lightning wallet and shoot it back off to a Bitcoin main wallet? I didn’t find that readily available anywhere and clearly listed, so here you go. 🙂
Continue reading “Closing out Lightning to Bitcoin”Bitcoin Node + Lightning Network + Tor
Okay, so this is the post that kickstarted me to return to StackAttack… because I’ll probably forget all of this in a week, and I want a reference. In short, the goal is:
- Setup a full Bitcoin core node
- Setup the Lightning Network Daemon
- Make it all work over Tor
Let’s dive in, shall we? 🙂
Continue reading “Bitcoin Node + Lightning Network + Tor”