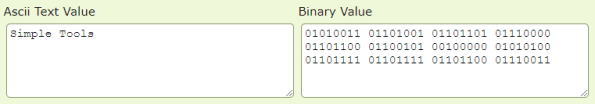
Just going to leave this here (and here) in case anyone needs a quick set of source-able functions to make quick ASCII->Binary and Binary->ASCII conversions from Linux command lines. 🙂
Identifying JTAG
This is a quick-hit post because as I’ve been working on some hardware hacking efforts I realized that while there are a lot of good resources on identifying JTAG interfaces and standards, there wasn’t really a good single page view of them. With that in mind, I lifted the following images from the excellent resource at http://www.jtagtest.com/pinouts/ and put them into a single page view. Full credit to JTAGtest… I just wanted something I could quickly reference.
Intro to Cryptography (Part 3 of 3)
This is the quick-hit version of the second of three parts of Introduction to Cryptography training I gave. As with all of the formal training, you can use the below for a quick reference, or view the full presentation here.
Intro to Cryptography (Part 2 of 3)
This is the quick-hit version of the second of three parts of Introduction to Cryptography training I gave. As with all of the formal training, you can use the below for a quick reference, or view the full presentation here.
Intro to Cryptography (Part 1 of 3)
This is the quick-hit version of the first of three parts of Introduction to Cryptography training I gave. As with all of the formal training, you can use the below for a quick reference, or view the full presentation here.
Firmware Analysis
This is the quick-hit version of the firmware analysis training I gave. As with all of the formal training, you can use the below for a quick reference, or view the full presentation here.
OSINT: Google and LinkedIn
This is the quick-hit version of the Open Source Intelligence (OSINT) training I gave on using data from Google and LinkedIn to profile an individual or organization. As with all of the formal training, you can use the below for a quick reference, or view the full presentation here: OSINT – Social Media (Google and LinkedIn) (basic_0x08)
Note: Do not use spaces between an operator (e.g. “-”) and the thing it operates on. For example:
bob -dylan # No Bob Dylan results
bob - dylan # Bob Dylan shows up in resultsBruteforcing ESSID Values
If you need to reveal an (E)SSID you can do this simply through MDK3. To do so we’ll use the “p” mode, as follows:
mdk3 {INTERFACE} p -f /path/to/file/of/potential_names -t {AP_MAC_ADDRESS} -b {CHARSET}For the “CHARSET” you can use “a” (for all characters, not recommended except for tiny names), or one or more of the following:
- u – Uppercase
- l – Lowercase
- n – Numbers
- s – ASCII symbols
Good hunting!
OSINT: Twitter and Facebook
This is the quick-hit version of the Open Source Intelligence (OSINT) training I gave on using data from Twitter and Facebook to profile an individual or organization. As with all of the formal training, you can use the below for a quick reference, or view the full presentation here: OSINT – Social Media (Facebook and Twitter) (basic_0x07)
Email Attachments
I was going through my old archives of files, exploits, and notes this week and came across a document I’d long since forgotten… a list of extensions I used to configure my mail hosts to block. I decided to give it a quick update to modernize some of the listings, and the resultant beast is 203 extensions. I wouldn’t say that everybody needs everything on this list, but if you’re looking for a one-stop list to be comprehensive I submit that this wouldn’t be a bad place to start.