So you want to build yourself one of those Pwnagotchi that everyone is talking about since the Flipper Zero came out and no one can get one, eh? And you’ve followed the official installation instructions (which this post supplements, but does not replace) but have noticed that either (1) you can’t really find a Waveshare eInk 2.13″ display that’s not version 3, or (2) you can’t quite seem to get into your Pwnagotchi if it’s even running and ERMAGERD WTF why is this so obtuse? Well, this is the guide for you. 🙂
Continue reading “Pwnagotchi Waveshare V3”Proxmark3 RDV 4
So… I got a Proxmark3 RDV 4 for Christmas. It’s great. It’s tiny, svelte, and… had a bunch of errors right out of the box. Naturally that means it’s time to reflash it, but as it turns out the default wiki instructions for Kali Linux aren’t quite right for the RDV 4 now. Let’s fix that, shall we?
Wireless Hacking
This is just a quick post to provide the presentation I gave tonight at PwnSchool. If you’d like to review it you can download it here. Thanks!
Topics covered:
- Introduction to Radio Frequency
- Wireless Hacking (WEP and WPA2)
- RFID Hacking (HID Prox and MIFARE)
- Bluetooth Hacking (Bluelog/bluesnarfer/Wireshark/etc)
Chuck Lumley
I maintain a modified version of Kali I use as the basis for my testing which includes a variety of extra tools, preference, references, etc. If you want a copy yourself, you can find one here:
https://drive.google.com/drive/folders/1id6hRacVUtcQRtq8zjSkxtTSE3AvxTk3?usp=sharing
Each version is named for a different character played by Henry Winkler, for the record.
QuickHit: wget Website Mirroring
You may often need to mirror all (or part) of a website for offline analysis. The ‘wget’ program has some easy features to use when you want to quickly get a local copy of a site and correct common issues (like links pointing to server locations). Set up one of these behind the scenes while you work on other aspects, then peruse at your leisure.
Update 2018-07-21: Or just use the script I wrote to simplify this for my customized Kali build, available here.
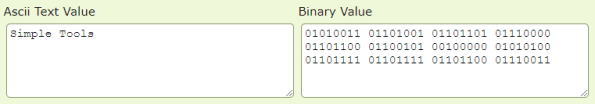
Quick ASCII Binary Tools
Just going to leave this here (and here) in case anyone needs a quick set of source-able functions to make quick ASCII->Binary and Binary->ASCII conversions from Linux command lines. 🙂
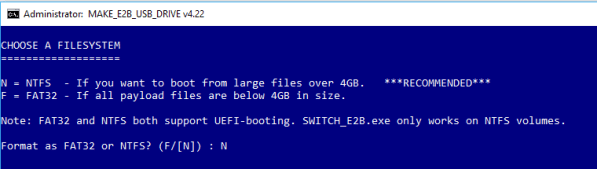
Multi-OS Boot Build
One of the most frustrating things to do is shuffle various USB drives trying to remember which one you were using last (for persistent OS boots), or which one has the working version of “X” operating system/which installer. This article covers how to take an external USB drive (whether a large thumb drive or an actual external hard drive) and turn it into a whizbang multi-OS booting device.
Benedict Slade
I maintain a modified version of Kali I use as the basis for my testing which includes a variety of extra tools, preference, references, etc. If you want a copy yourself, you can find one here:
https://drive.google.com/open?id=1X0IHNuRCWjHoQdvQUaEwWoDLKEB1_5ti
CTF-Tools
I’ve started tracking individual CTF and other tools that I typically add to distributions to my standard GitHub. If you want/need to pull any of these they are located here:
Bruteforcing ESSID Values
If you need to reveal an (E)SSID you can do this simply through MDK3. To do so we’ll use the “p” mode, as follows:
mdk3 {INTERFACE} p -f /path/to/file/of/potential_names -t {AP_MAC_ADDRESS} -b {CHARSET}For the “CHARSET” you can use “a” (for all characters, not recommended except for tiny names), or one or more of the following:
- u – Uppercase
- l – Lowercase
- n – Numbers
- s – ASCII symbols
Good hunting!