I realized I didn’t have any good notes on Radio Frequency Identification (RFID) tags/badges/etc, so I figured it was time to compile that and update it while I’m at it. This post is just a quick run-down of the frequencies, types, and common cards/IDs. If you don’t know what an RFID is, for the purposes of most pentesting it’s a security badge or a key fob, like you can see in the image at the top of this posting.
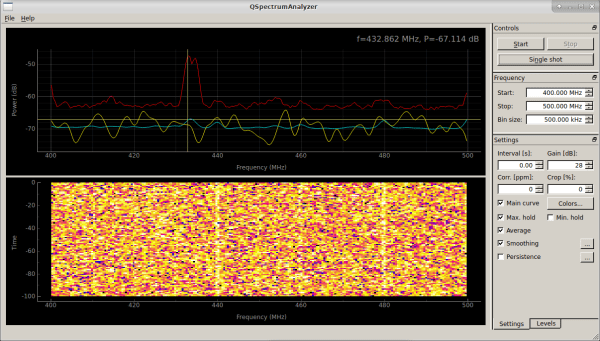
Getting Started with the HackRF
I have to teach some folks how to find, isolate, and analyze signals tomorrow, which of course means this is the perfect time to document some quick steps for my own reference. I started the build out from the DEFCON 26 Hardware Hacking Village Kali Live Build. If you don’t have it your mileage may vary… on to the buildout.
Backpack Pentesting
I made a presentation a few months ago based on a simple question I relieved… “What is all that stuff in your backpack?” I normally carry, well, more than I really need. Full list with links is below, or here’s the presentation for those who want to see it in all its original, horrible glory. Ever wonder what types of stuff I normally carry when on a pentest? Well, now you know. Enjoy!
QuickHit: wget Website Mirroring
You may often need to mirror all (or part) of a website for offline analysis. The ‘wget’ program has some easy features to use when you want to quickly get a local copy of a site and correct common issues (like links pointing to server locations). Set up one of these behind the scenes while you work on other aspects, then peruse at your leisure.
Update 2018-07-21: Or just use the script I wrote to simplify this for my customized Kali build, available here.
TILFH: Quotes and When to Use Them
One thing that always confuses me when I’m writing Bash scripts is what type of quote to use in a given situation. Luckily, Hermit schooled me with this quick rundown:
“SOMETHING” = This means evaluate what’s between the quotes.
‘SOMETHING’ = This means don’t evaluate what’s between the quotes. This is a literal string.
`SOMETHING`= This means execute the stuff between the quotes and spit out the result. NOTE: These little back quotes are hard to find. Look on the tilde key.
$(SOMETHING) = Same as above.
– Killswitch
Random Characters
Because every so often it’s nice to have a list of characters you can just copy/paste from, rather than trying to figure out where else they may be.
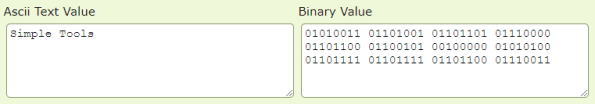
Quick ASCII Binary Tools
Just going to leave this here (and here) in case anyone needs a quick set of source-able functions to make quick ASCII->Binary and Binary->ASCII conversions from Linux command lines. 🙂
PenTest Aliases and Setup
I like to setup a few things when I’m building an image for a pentest. They’re helpers that keep me honest, because without them I’d likely forget something or miss some detail, and by establishing consistent patterns I reduce that risk. To start with, I make a consistent directory structure. For the sake of this article, let’s call it:
/engagementNext up, I generate some subfolders which are critical to my process:
Continue reading “PenTest Aliases and Setup”
Identifying JTAG
This is a quick-hit post because as I’ve been working on some hardware hacking efforts I realized that while there are a lot of good resources on identifying JTAG interfaces and standards, there wasn’t really a good single page view of them. With that in mind, I lifted the following images from the excellent resource at http://www.jtagtest.com/pinouts/ and put them into a single page view. Full credit to JTAGtest… I just wanted something I could quickly reference.
Intro to Cryptography (Part 3 of 3)
This is the quick-hit version of the second of three parts of Introduction to Cryptography training I gave. As with all of the formal training, you can use the below for a quick reference, or view the full presentation here.