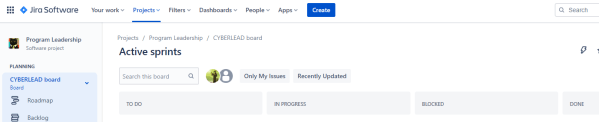
Over the past seven-ish years I’ve developed my own system for managing work from an executive perspective down to the individual contributor, and after some prompting from a friend (thanks MadHat!) I realized this might be helpful to others. Just to level set, the intent of this approach is to grow a full work management solution from nothing to the point where you can dynamically manage workloads and commitments, and to do so in a continuously evolving and improving way. As with anything agile… fail early, fail often, and go with what works for you and your teams. 🙂
Continue reading “Jira for Business Management”Pwnagotchi Waveshare V3
So you want to build yourself one of those Pwnagotchi that everyone is talking about since the Flipper Zero came out and no one can get one, eh? And you’ve followed the official installation instructions (which this post supplements, but does not replace) but have noticed that either (1) you can’t really find a Waveshare eInk 2.13″ display that’s not version 3, or (2) you can’t quite seem to get into your Pwnagotchi if it’s even running and ERMAGERD WTF why is this so obtuse? Well, this is the guide for you. 🙂
Continue reading “Pwnagotchi Waveshare V3”Custom Proxmox VE LXC Images
Using Linux Containers can significantly improve deployment times to make customized instances of a system. For instance, you may want to create 10 unique instances of a system for training purposes, but don’t want to run custom code on each when it starts to generate key material, assign users, etc. Using Linux Containers can make that simple, but unfortunately it’s not always so simple to create that custom image for deployment. This post is going to cover the start to finish customization of an image (in this case, using Kali Linux) from the base image to one that can deploy in a non-privileged virtualization platform (in this case, Proxmox VE). Let’s get started!
Continue reading “Custom Proxmox VE LXC Images”Starting the 2020 eChallenge Coin Redux
There’s a designer named Bradán Lane who makes some excellent hardware, and one of my favorite things he’s created is a set of challenge coin circuits. I won’t go into too much detail on them other than to note they have a fun story line, a series of challenges, and you have to exercise some basic hardware hacking skills to participate. If you’d like more details, please check out the listing for the coin on Tindie. But what if you don’t know how to get started? Well, a friend of mine (Visual) and I recently played through this, and thought we’d document how to get started for anyone who needs a little extra help. Let’s get started!
Continue reading “Starting the 2020 eChallenge Coin Redux”DerbyCon 9 – TrustedSec Challenge Coin Solution
This last weekend was the final DerbyCon. We’ll #TrevorForget. It was also an event filled with several quick and fun CTFs… and since I’ve been deficient in posting things lately, I figured I’d catch up by showing how to solve a whole pile of them. First up: the TrustedSec Challenge Coin! Attendees could get one of these by just showing up and asking for one, and there was a prize pack being awarded to anyone who could solve it. I was the fifth to do so, and figured others might want to know how to get to the final message.
Continue reading “DerbyCon 9 – TrustedSec Challenge Coin Solution”
Analyzing Multiple APKs At Once
This falls into that series of things where I had to make something work when there wasn’t a pre-built package, so I’m documenting it here in case (1) I ever need to do this again, or (2) someone else can benefit from it. Let’s say you’re looking into a device that runs on Android, and it has a bunch of APKs that you have no clue what to do with… why not use some common tools to quickly process all of those files?
Wireless Hacking
This is just a quick post to provide the presentation I gave tonight at PwnSchool. If you’d like to review it you can download it here. Thanks!
Topics covered:
- Introduction to Radio Frequency
- Wireless Hacking (WEP and WPA2)
- RFID Hacking (HID Prox and MIFARE)
- Bluetooth Hacking (Bluelog/bluesnarfer/Wireshark/etc)
QuickHit: wget Website Mirroring
You may often need to mirror all (or part) of a website for offline analysis. The ‘wget’ program has some easy features to use when you want to quickly get a local copy of a site and correct common issues (like links pointing to server locations). Set up one of these behind the scenes while you work on other aspects, then peruse at your leisure.
Update 2018-07-21: Or just use the script I wrote to simplify this for my customized Kali build, available here.
Getting Started with DigiSpark
I bought a pile of DigiSpark devices on a whim (they’re less than $2 each), and the following are just my notes on how to get things up and running with them to do simple testing. I’ll also note that this was based on the DigiStump connecting tutorial, but I found some gaps in their approach and wanted to document my variations here for posterity.
MSF Fundamentals 2017 (Part 1 of 3) – Console to Payload
This is quick-hit version of part one of a three part series on Metasploit Fundamentals that I wrote to update my previous work (from 2014) on Metasploit. If you’re looking for a more hands-on/in-depth version of this article you can access training on this topic here: MSF Fundamentals – Part 1 of 3 (Startup Exploit Payload) (basic_0x02)
The purpose of this article is to get you familiar with starting up the Metasploit Framework (MSF), finding an exploit, finding a matching payload, and configuring everything up until it’s time to launch an exploit. Part two will cover exploitation and post-exploitation modules, while part three will cover pivoting, lateral movement, and automation. This training assumes you’re using a 2016 variant of Kali Linux and that it’s patched up to at least August 2016. If that’s true, then let’s go!
Continue reading “MSF Fundamentals 2017 (Part 1 of 3) – Console to Payload”