I had some requests to provide my take on the OSI model separately from the presentation I made at PwnSchool, so here you go… the most comprehensive, authoritative version of the OSI model ever presented.
First up, a definition. The Open Systems Interconnect (OSI) model provides a way to conceptualize communications. In particular, it describes how to go from the most specialized form of information down to the least specialized (a phyiscal connection) and then back to the most specialized form. It also does so by providing the concept of encapsulation, meaning that more specialized data is contained as a portion of less specialized data. That might be a bit confusing, so we’ll dive into it in more detail.
When dealing with the OSI model we speak of it in terms of layers. The lower the layer number, the closer the information is to the hardware, and the less specialized it is. In general we can make a break between layers four and five; if we’re talking about layers 1 through 4 we’re talking about how data moves around, and if we’re talking about layers 5 and up we’re talking about what the data is or means.
As one final note, I’m going to use two terms quite specifically in this posting:
- Information is anything that IS useful to the current layer.
- Data is anything that IS NOT useful to the current layer.
The “Standard” OSI Model
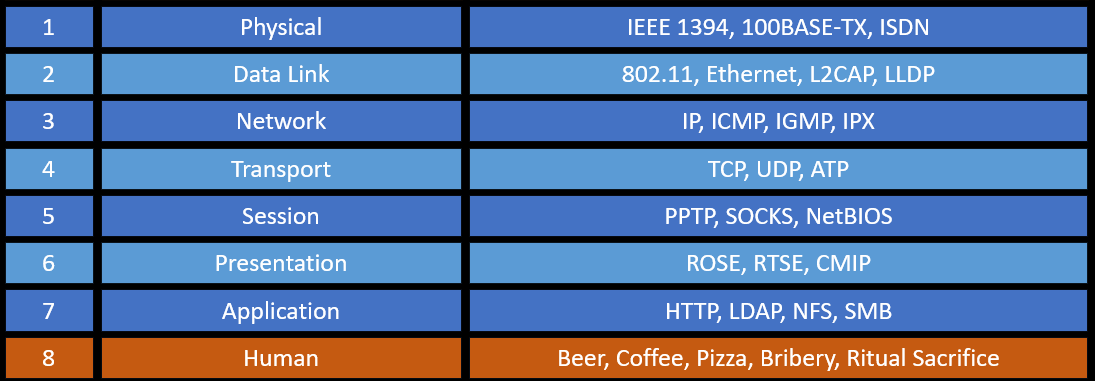
The “standard” OSI model layers are as follows:
- Layer 1: Physical
The first layer is literally the physical connection between two or more systems. It may be a cable, an RF transmission, or even air currents and Carrier pigeons in one particular instance (RFC 1149). - Layer 2: Data Link
The second layer is concerned with the way that data is transmitted over a physical layer. It only deals with how units of data are put together for transmission, and nothing else. Two common example of this are Ethernet and WiFi, each of which specifies how to signal the duration of a transmission, the spacing between transmissions, etc, but neither of which species anything about the content of those transmissions. - Layer 3: Network
The third layer takes care of addressing and grouping senders and receivers. The Data Link layer doesn’t care if you are talking to a system eight inches of wire away or around the world. The Network layer only deals with how to identify who is sending data, who should receive it, and how each can communicate logically. - Layer 4: Transport
The fourth layer is only concerned with whether or not data gets to its destination. That’s it. In the case of Transmission Control Protocol (TCP) it makes certain that delivery occurs. In the case of User Datagram Protocol (UDP) it makes certain that data is sent out, but that’s it. In short, it acts like DHS, FedEx, or your cousin Ryker. Some of those may be reliable, some may cost more, and some may or may not ever get to where they were going. - Layer 5: Session
The fifth layer deals with which strand of communication we are talking about. Think of this like email threads or conversations. Your email system as a whole delivers messages to you, and some are part of threads/conversations, while others are completely standalone. In reality, it’s more about multiple connections, but the email idea is what I’ve found is generally best to describe this. - Layer 6: Presentation
The sixth layer deals with conversion of data from one format to another. Note that this is not application-specific data (e.g. PDF being opened by Word) but rather data format information (e.g. converting from one character format to another, such as is done by Telnet). - Layer 7: Application
The seventh layer (which is the last one officially defined) deals with “everything else” and is the layer that humans interact with.
If you’re ever being interviewed you can remember this with “People Don’t Need Those Stupid Packets Anyways” (or if you favor a giggle the more colorful “Please Do Not Touch Superman’s Private Area”).

Now, on to the “Professional” OSI Model!
The “Professional” OSI Model
The “Professional” OSI model introduces three additional layers:
- Layer 8: Human
The eighth layer is concerned with what people do, and how they interact with computers. Commonly known as the most vulnerable layer, it has its own unique sets of protocols, with the most common joke protocols being Beer, Pizza, Coffee, Bribery, and Lust. - Layer 9: Organization
The ninth layer is concerned with how groups of humans interact towards a particular goal, and is the organization. You can think of the ninth layer as encapsulating three through seven from the standard OSI model but with humans substituting for systems and processes for applications. - Layer 10: Government
The tenth layer is concerned with how groups of organizations interact within a society, and is the government. You can think of the tenth layer as encapsulating layers three through seven from the standard OSI model but with organizations substituting for systems and regulations for applications.
All of this can now be brought together into the following model. I’ve confusingly shown this from lowest level to highest for clarity of discussion, but by convention we talk about lower numbers as being “down” the stack, and higher numbers as being “up” the stack, so I’ll use that convention in this article as well.

Encapsulation Example
So how do we mix these things together? We use something called encapsulation. If you’ve ever seen Russian nesting dolls (Matryoshka) then you’re already familiar with the concept.

Put more simply, the smallest doll is the application layer, which goes into a bigger doll (presentation layer), then a bigger doll (session layer), and so on. Each layer handles its small chunk of work, and then either moves further up the layers (by removing the outer doll in this example) or further down the layers (by going into a new doll).
All that being said, these concepts still probably doesn’t make a ton of sense — at least if this is your first time thinking about this — so let’s further break that down using an email experience via Outlook (or any other email client) as an example.
Email Client Example
Let’s walk through an example now showing how all of this ties together. We’ll start in our email client, which has two accounts (elite@ctf.domains and n00b@ctf.domains) added to it. We’ll then send an email between them to demonstrate the approach, and for simplicity assume that they’re on the same switch and in the same network as the mail server.
- Layer 7 (Application): We draft our email from “elite” to “n00b” and hit the Send button.
- Layer 6 (Presentation): There’s nothing to do here, so we move on.
- Layer 5 (Session): The operating system sees an open connection for “elite” to the mail server and adds the session information around the email.
- Layer 4 (Transport): The operating system chunks up the email into discrete pieces for transmission — which we’ll call packets — and handles error correction and re-transmission methods to make sure it gets to its target. This information is added to each packet.
- Layer 3 (Network): The operating system adds on the address information for the mail server as a destination, and itself as the source or sender.
- Layer 2 (Data Link): The data is further broken up into chunks specific to the data link — in this case Ethernet — which we’ll call frames. Each unit of data then has information added to it to communicate how the splitting was accomplished and can be reversed.
- Layer 1 (Physical): The framed data is converted into electrical pulses on a wire and goes out to the switch. This information is received at the destination mail server which converts those electrical pulses back into framed data. The mail server sends the result up the model stack.
- Layer 2 (Data Link): The framing information is removed and the data is reassembled and passed up the model stack.
- Layer 3 (Network): The destination is verified as accurate and removed, and the data is passed up the model stack.
- Layer 4 (Transport): The information is used to verify that the data received matches the data that was sent, and confirmation of receipt is sent back down the stack. The packets themselves are reassembled into the original data and passed up the model stack.
- Layer 5 (Session): The data is checked to confirm it matches a known session, then the session information is removed and the data is routed into the appropriate stream of communication and passed up the model stack.
- Layer 6 (Presentation): The data is verified to be in the same format as the program is expecting (no translation is required), so the data is passed up the model stack.
- Layer 7 (Application): The email server receives the information and sends confirmation back to the client… the process repeats, switching the source and destination.
And so on and so on and so on. A never-ending, often forking, stream of data moving up and down through the model. A few final thoughts to point out:
- It’s entirely possible for a data flow to move both up and down the stack. For instance, when a system receives data the TCP protocol both passes information up the stack (headed towards an application) as well as down (to confirm receipt to the local system).
- It’s entirely possible for multiple protocols/handlers to exist at the same layer for layers five and above. For layers eight and above it’s almost mandatory.
- We say “encapsulation” to make it easy, but in reality this can be either via a header/footer combination (e.g. information added before and after a chunk of data) as well as purely through a header (e.g. information added only before a chunk of data).
That’s it! Good hunting!

Leave a comment